Over time, your business will accumulate a lot of data, including some that certain employees or departments will have no need to see (or perhaps...
Reciprocal Technologies Blog Security • Page 27
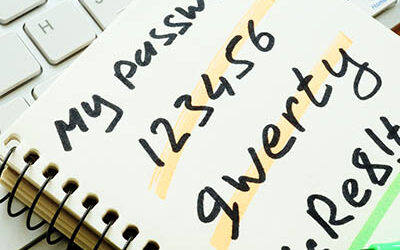
Start Off 2020 by Auditing Your Online Accounts and Passwords
Let’s take a look at a real-world scenario that I ran into a few weeks ago with a family friend. For the sake of this story, let’s call him Bob. Bob...
These Are the Last Days of Windows 7
Microsoft is just days away from retiring not just one, but two of its most popular operating systems. The software giant has made a point to run a...
Security Has to Be a Priority in 2020
Cybercriminals aren’t exactly holding back when it comes to attacking businesses, which means that businesses can’t rest on their haunches as the...
A Recent Data Theft Shows Us What to Watch Out For
Trend Micro, the developer of the popular antivirus program, has attracted some unwanted attention after a former employee managed to steal customer...
Start Using Two-Factor Authentication Everywhere, Today
It can be easy to slack off when it comes to good password practices. Many users still use the same password across multiple sites and often don’t...
How to Optimize Security, Regarding Your Servers
Your business relies on its servers in order to function - which makes it incredibly important that these servers are sufficiently protected. There...
Cybersecurity is a Shortcoming for the DHS
Every IT administrator today needs to be concerned about cybersecurity, as does every private business when it comes to its network. However, the...
Tip of the Week: Mobile Data Management
There are hundreds of things that a business owner has to do, so managing the security of the data coming in and going out from mobile devices might...
How Google is Trying to Make Passwords Easier and Better
Common opinion more or less states that passwords aren’t so much “necessary,” as they are a “necessary evil.” The best practices that are...